CrowdStrike Next-Gen SIEM
Support Statement
This documentation is provided "as is" without support for 3rd party software. The level of support for this integration guide is best effort without any SLA on response time. No 3rd party product support can be provided by Superna directly. 3rd party components require support contracts. See EULA for more details.
Overview
Superna Data Security Edition integrates with CrowdStrike Next-Gen SIEM to stream security findings from the storage layer directly into the Falcon platform for search, correlation, and alerting. When Superna detects malicious activity - it automatically forwards those findings to CrowdStrike Next-Gen SIEM via the Collector API, where they appear as searchable log events and detections alongside other security telemetry.
For ransomware detection, all required indicators are preconfigured by Superna and do not need to be recreated in the SIEM. Each payload contains the necessary details for the SecOps team to assess the event, conduct investigations, or build correlation rules with detections from other security systems.
Demo Video
Features and Solution Overview
This integration provides the following capabilities:
- Structured log ingestion — Superna findings are forwarded to CrowdStrike Next-Gen SIEM via the Collector API, mapped to CrowdStrike Parsing Standard (CPS) format for native compatibility.
- Detections visibility — high-confidence findings surface as detections in the CrowdStrike Falcon console for SOC review and triage.
- Rich incident context — each webhook payload includes the actor username, client IP addresses, affected SMB shares, file paths, severity, and detection state so the SOC can immediately assess scope.
Customer Workflow Benefits
- Correlate Superna's storage-layer detections with endpoint, identity, and network signals already in Next-Gen SIEM.
- Reduce mean time to detect and respond (MTTD/MTTR) by centralizing storage security findings in a single pane of glass.
- Build saved searches, alerts, and correlation rules in Next-Gen SIEM based on Superna event fields.
Limitations
- Requires a CrowdStrike Next-Gen SIEM subscription with Data Onboarding entitlement.
- The integration runs as a service on the Superna (Eyeglass) VM and requires direct outbound HTTPS connectivity from the VM to CrowdStrike. HTTPS proxy routing is not supported.
- Upgrade and rollback functionality is not available.
About CrowdStrike Next Gen SIEM
CrowdStrike Falcon Next-Gen SIEM revolutionizes threat detection, investigation, and response by bringing together unmatched security depth and breadth in one unified platform. It combines log ingestion, search, correlation, and detection capabilities natively within the Falcon platform, eliminating the need for separate SIEM infrastructure. The Superna data source is available directly within the Next-Gen SIEM Data Onboarding tab via the CrowdStrike Marketplace.
Prerequisites
Before beginning, ensure the following requirements are met:
Superna Requirements
- Superna Data Security Edition - version 2.13.0 or later is recommended for built-in webhook test button
- Active Superna license with Zero Trust / Data Security features enabled.
- Superna (Eyeglass) VM running Linux with systemd
- Minimum 1 GB free disk space on the Eyeglass VM.
- Root (sudo) access to the Eyeglass VM.
CrowdStrike Requirements
- CrowdStrike Next-Gen SIEM subscription with Data Onboarding entitlement.
- Superna Crowdstrike Connector is available in Crowdstrike marketplace here
- The Superna data source connector must be created in Next-Gen SIEM first (see details below) to obtain the required API URL and API Key.
Network Connectivity
- The Superna VM must have outbound HTTPS (port 443) access to your CrowdStrike API endpoint (api.crowdstrike.com or regional equivalent).
- No inbound firewall rules are required for this integration.
- HTTP/HTTPS proxy routing is NOT supported. Direct connectivity is required.
Installation
Configure the Superna Data Connector in CrowdStrike Next-Gen SIEM
Before installing the Feature Pack, you must set up the Superna data source connector in CrowdStrike Next-Gen SIEM to obtain the API URL and API Key needed to configure the integration.
- Log in to the CrowdStrike Falcon console.
- Navigate to Next-Gen SIEM → Data Onboarding.
- In the Data Source Search box, type Superna.
- Click the Superna Data Security Edition connector.
- Fill in the required fields and click Save.
- When prompted, click Generate API Key. Copy and securely store this key - it is shown only once.
- Navigate to Data Sources, click on the newly created data source, and record the API URL (ingest endpoint URL). Save this URL for the Feature Pack configuration step.
The API URL format is typically: https://<id>.ingest.<region>.crowdstrike.com/services/collector
The region matches your Falcon tenant (e.g., us-2, eu-1).
Download the Installer
-
Download the Feature Pack installer file
crowdstrike-siem-v1.0.0.runfrom the Superna support portal.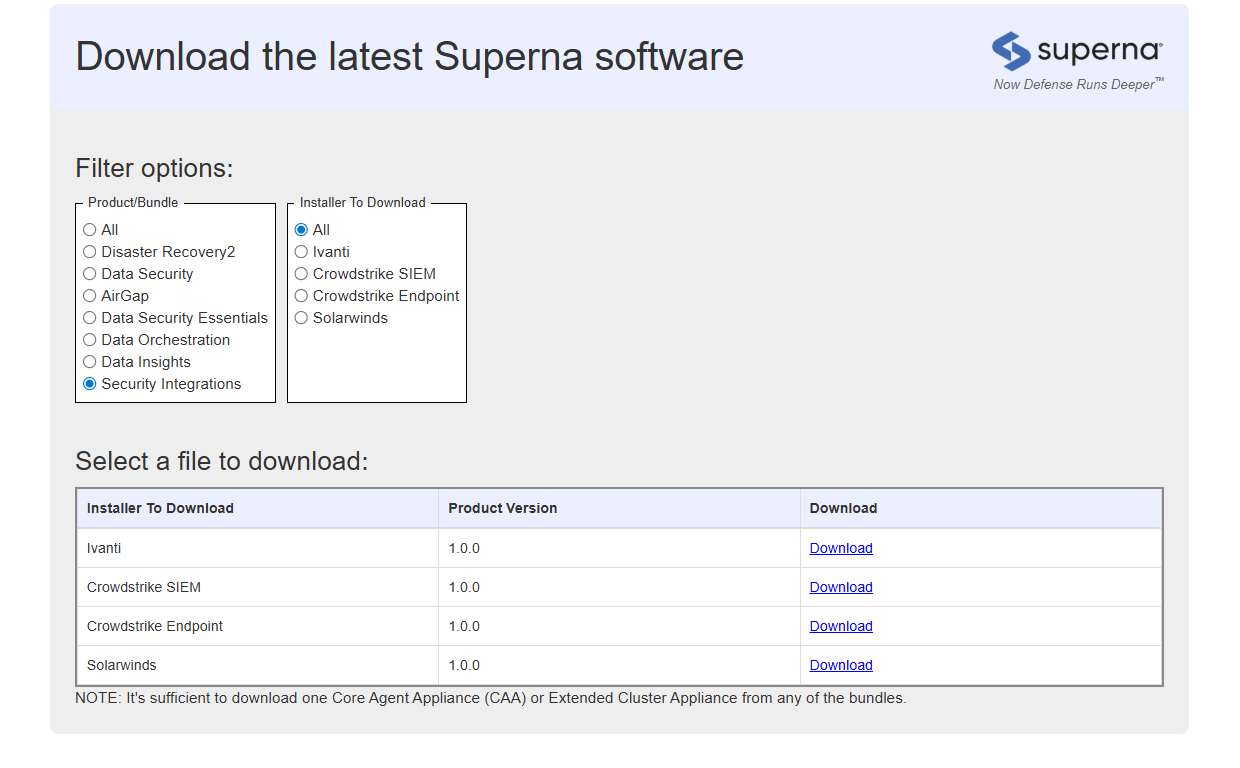
-
Transfer it to the Eyeglass VM using SCP or your preferred secure file transfer method:
scp crowdstrike-siem-v1.0.0.run user@your-eyeglass-vm:/tmp/
Make the Installer Executable
SSH into the Eyeglass VM, navigate to the installer location, and set the executable bit:
ssh user@your-eyeglass-vm
cd /tmp
chmod +x crowdstrike-siem-v1.0.0.run
Run the Installer
The installer provides an interactive Text User Interface (TUI). Root (sudo) is required.
sudo ./crowdstrike-siem-v1.0.0.run
TUI Keyboard Navigation
| Key | Action |
|---|---|
| Tab | Navigate between fields |
| Enter | Edit field / Confirm selection |
| Esc | Exit field (enables keyboard shortcuts) |
| V | Validate all fields |
| I | Install (press Esc first to exit any active field) |
| Q | Quit installer |
| H | Show help |
Installation Workflow
- Fill in the required configuration fields (see table below).
- Press Esc to exit the active field, then press V to validate all fields.
- Review any validation errors and correct them.
- Press Esc, then press I to start the installation. Confirm when prompted.
Required Configuration Fields
| Field | Description | Example |
|---|---|---|
| CrowdStrike Collector API URL | Ingest endpoint URL from the Next-Gen SIEM data source | https://<id>.ingest.us-2.crowdstrike.com/services/collector |
| CrowdStrike API Key | API Key generated from the Superna connector in Next-Gen SIEM (masked in TUI) | (masked) |
| Eyeglass Host IP Address | IP of the Superna Eyeglass VM | 10.0.0.50 |
| Webhook Port | Local port for the webhook listener (auto-assigned if conflict) | 5000 |
| Install Default Webhook | Auto-register webhook in Superna Data Security Edition | true (recommended) |
The installer automatically detects port conflicts and assigns the next available port if the requested webhook port is already in use by another integration.
Preview / Dry Run (Optional)
To preview what the installer will do without making any system changes, run:
sudo ./crowdstrike-siem-v1.0.0.run --dry-run
Verify Service Status
After installation completes, confirm the integration service is running:
sudo systemctl status crowdstrike-siem.service
Expected output:
● crowdstrike-siem.service - CrowdStrike Next-Gen SIEM Integration
Loaded: loaded (/etc/systemd/system/crowdstrike-siem.service)
Active: active (running) since ...
Configuration
Configure Superna Webhooks
If Install Default Webhook was selected as true during installation, the webhook is already registered automatically. You can review or adjust the configuration at:
Integrations → Webhooks → crowdstrike-siem
Recommended webhook filter settings:
- Severities: Critical and Major events only.
- Events / Lifecycle states: LOCKED_OUT and DELAYED_LOCKOUT (events that signal active containment decisions).
- Event types: THREAT_DETECTION.
In Enforcement mode, only Critical and Major events are generated. In Monitor mode, Warning events are generated. Align your webhook filter to your operating mode to avoid alert fatigue.
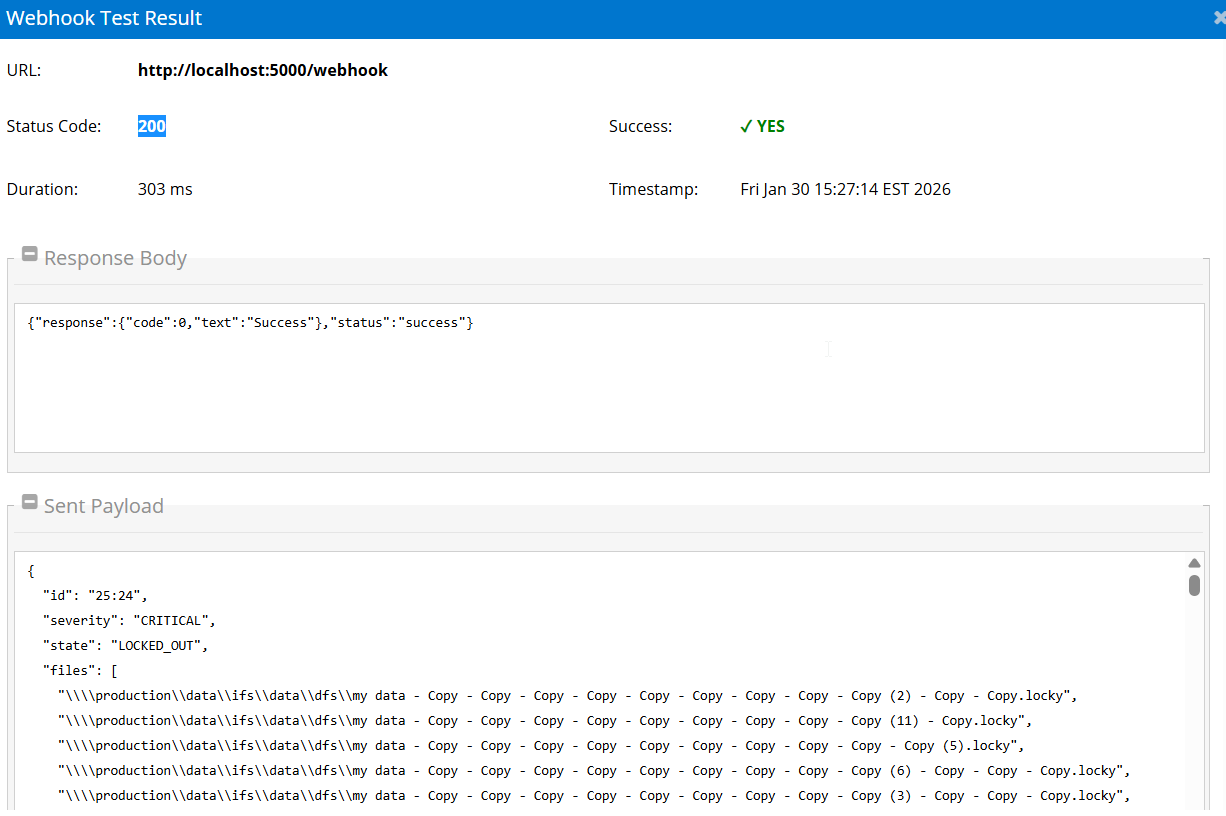
Test the Integration
For Superna Data Security Edition 2.13 and later:
- Log in to the Superna Data Security Edition web interface.
- Navigate to Integrations → Webhooks.
- Locate the crowdstrike-siem webhook entry.
- Click the Test Webhook button.
- Verify HTTP response code 200 or 201 is returned. Any other response indicates a configuration issue.
Send a sample payload manually using a sample curl command.
Modify Configuration After Installation
Run the installer again to make any changes in your configuration.
SecOps Administrator Integration Experience
How the Integration Works End-to-End
Once the integration is fully configured, the event flow is as follows:
- Detect — Superna Data Security Edition identifies a threat at the storage layer (e.g., ransomware patterns, mass deletion, anomalous SMB activity).
- Trigger — Superna's webhook posts an event payload to crowdstrike-siem service on the Eyeglass VM. The payload includes severity, user, client IP addresses, affected shares, and file paths.
- Translate — The service translates the Superna payload into CrowdStrike Parsing Standard (CPS) format and forwards it to the CrowdStrike Collector API using the configured API key and ingest URL.
- Ingest — CrowdStrike Next-Gen SIEM receives the event and makes it available in Investigate → Event Search as a parsed, searchable log entry.
- Alert — High-confidence findings surface as detections in the Next-Gen SIEM console. SOC analysts can investigate, correlate with other signals, and respond.
What Administrators Will See in CrowdStrike Next-Gen SIEM
- Events appear in Investigate → Event Search, searchable and filterable by vendor ("Superna"), severity, user, shares, files, and client IP.
- Detections generated from Superna findings are visible in the Falcon Detections console for SOC triage.
- All forwarded events are in CPS format, enabling native correlation with CrowdStrike Next-Gen SIEM.
- Saved searches and custom alerts can be built in Next-Gen SIEM based on any Superna event field (e.g., alert on any event where severity = CRITICAL).
Recommended Response Workflow
- Receive notification — a detection or saved search alert fires in CrowdStrike Next-Gen SIEM based on a Superna finding.
- Review the Superna event — in Event Search, examine the full event fields: which user triggered the alert, what files and shares were affected, client IP addresses, and current state (LOCKED_OUT, DELAYED_LOCKOUT).
- Correlate with endpoint signals — pivot from the client IP or username to CrowdStrike Falcon Insight (EDR) data in the same platform to review process activity, network connections, and file events on the host.
- Correlate with identity signals — cross-reference the Active Directory user from the Superna event with identity and authentication logs in Next-Gen SIEM.
- Correlate signals — combine Superna's storage-layer view (files encrypted, mass deletes) with Falcon's endpoint-layer view (malicious process, lateral movement).
- Respond — take action using available tools: trigger host containment via the EDR integration, run playbooks via Falcon Fusion SOAR, or escalate to Tier 2/3.
- Remediate and close — once the host is clean, release any lockouts made by Superna and close the detection.
Building Saved Searches and Alerts in Next-Gen SIEM
Use the following example searches in Next-Gen SIEM Event Search to build saved queries or alerting rules:
All Superna events:
vendor=Superna
Critical severity events only:
vendor=Superna severity=CRITICAL
Locked-out hosts:
vendor=Superna state=LOCKED_OUT
Events involving a specific user:
vendor=Superna userName=<username>
Integration Architecture
Troubleshooting
Useful Commands
Check real-time service logs:
sudo journalctl -u crowdstrike-siem.service -f
Start / Stop / Restart:
sudo systemctl start crowdstrike-siem.service
sudo systemctl stop crowdstrike-siem.service
sudo systemctl restart crowdstrike-siem.service
sudo systemctl status crowdstrike-siem.service
Enable / Disable Auto-Start on Boot:
sudo systemctl enable crowdstrike-siem.service
sudo systemctl disable crowdstrike-siem.service
Review Installation Logs:
ls -la /opt/superna/sca/logs/crowdstrike-siem-fpk-install-20260115-163142.log
View last 100 log lines:
sudo journalctl -u crowdstrike-siem.service -n 100
Save logs to a file for review:
sudo journalctl -f -n 250 -u crowdstrike-siem.service > /tmp/crowdstrike-siem.log
nano /tmp/crowdstrike-siem.log
View webhook registration:
sudo cat /opt/superna/sca/data/eventWebhook.json | jq .
Common Misconfigurations
| Issue | Likely Cause | Resolution |
|---|---|---|
| Service fails to start | Missing or invalid config.env values | Check config.env; verify CROWDSTRIKE_COLLECTOR_URL and CROWDSTRIKE_API_KEY are correct. Restart service. |
| Webhook returns non-200 response | Service not running or port mismatch | Run: systemctl status crowdstrike-siem.service. Check the webhook URL port matches WEBHOOK_PORT in config.env. |
| Events not appearing in Next-Gen SIEM | Wrong Collector API URL or stale API key | Verify CROWDSTRIKE_COLLECTOR_URL matches the URL from the Superna data source in Next-Gen SIEM. Regenerate the API key if expired. |
| HTTP 401 from Collector API | Invalid or expired API Key | Regenerate the API key in Next-Gen SIEM Data Sources, update config.env, and restart the service. |
| HTTP 403 from Collector API | API key lacks permission or wrong data source | Ensure the API key was generated from the correct Superna data source connector in Next-Gen SIEM. |
| Cannot reach Collector API endpoint | Firewall blocking outbound HTTPS from VM | Verify outbound port 443 is open from the Eyeglass VM. Proxy is not supported. |
| Wrong region in Collector API URL | URL does not match your Falcon tenant region | Confirm your Falcon tenant region (e.g., us-2, eu-1) and use the matching ingest URL from Next-Gen SIEM Data Sources. |
| Port conflict during installation | Requested webhook port already in use | The installer auto-detects and assigns the next available port. Check the installation log and verify WEBHOOK_PORT in config.env. |
Debugging Steps
- Verify the service is running:
systemctl status crowdstrike-siem.service. - Check service logs for errors:
journalctl -u crowdstrike-siem.service -n 50. - Validate config.env contains the correct Collector API URL and API Key.
- Test Collector API connectivity using the curl command.
- Send a manual test webhook and verify the service log shows HTTP 200 with successCount: 1.
- Log in to CrowdStrike Next-Gen SIEM and search for
vendor=Supernato confirm events are arriving. - Contact Superna support with service logs if the issue persists.
FAQs
What's required to enable this?
A Next-Gen SIEM data connector in Falcon (to obtain the API URL and API key), an Eyeglass VM with outbound HTTPS, and Superna webhook configuration. Installation takes approximately 15-20 minutes using the automated installer.
Which fields are forwarded?
Common fields include eventid, host (from clientIPs[0]), severity, state, nes, user, userName, shares[], detected (seconds), protocol, and files[]. Events are mapped to CrowdStrike Parsing Standard (CPS) format for native compatibility.
Is there a performance impact?
Minimal. The service makes small HTTPS posts to the collector API. Scope webhooks to critical/meaningful findings (Critical and Major severities recommended) to minimize event volume and avoid alert fatigue.
Any common pitfalls?
Using the wrong ingest URL/region, stale API key, blocking outbound HTTPS, or sending low-signal alarms instead of high-confidence findings. Always verify the API URL region matches your Falcon tenant region.
Can I use an HTTP proxy?
No. HTTP/HTTPS proxy routing is not supported. The integration requires direct outbound HTTPS connectivity from the Eyeglass VM to CrowdStrike.
How do I upgrade the integration?
Upgrade and rollback functionality is not available. To modify the configuration, run the installer again with updated settings.
What happens if the service stops?
Events will not be forwarded to CrowdStrike until the service is restarted. The service is configured to auto-start on boot via systemd. Check service status with systemctl status crowdstrike-siem.service.
How do I build correlation rules in Next-Gen SIEM?
Use the Event Search interface to build saved searches based on Superna event fields. Examples: vendor=Superna severity=CRITICAL or vendor=Superna state=LOCKED_OUT. You can create alerts from saved searches to trigger notifications or automated response actions.